The 9 Security Metrics Every CISO Must Track (And Why Most Cannot)
TLDR
Most security leaders at SLTT governments, healthcare systems, and nonprofits know which metrics their boards and auditors want to see. The problem is that shadow IT, resource constraints, and inadequate tools create a visibility gap that makes accurate measurement impossible regardless of intent. This piece identifies the nine metrics that translate security operations into evidence boards and regulators to accept, explains why the visibility gap blocks most organizations from tracking them, and shows what closing that gap requires.
What You Need to Know:
- Most security leaders at SLTT governments, healthcare systems, and nonprofits cannot track the metrics their boards and auditors require because shadow IT and inadequate tools make their own network invisible to them.
- The 9 metrics covered here translate security operations into evidence boards, auditors, and regulators accept.
- 60% of data breaches exploit vulnerabilities that already had a patch available, making patch compliance tracking one of the highest-leverage metrics a security leader can own.
- Closing the visibility gap is a prerequisite for accurate measurement, not a separate initiative.
- Part 2 explains how to close the measurement gap with agentless monitoring technology designed for resource-constrained security teams.
- Prefer to listen? This blog is the companion to Episode 7 of the Cyber Resilience Report — available on Apple Podcasts, Spotify, YouTube, and Amazon Music.
What Are the 9 Security Metrics Every CISO Must Track?
The 9 security metrics every CISO must track are: Endpoint Detection Coverage, Patch Compliance Rate, Percent of Critical Vulnerabilities Open Past SLA, Vulnerability Remediation Time, Incident Volume, MFA Coverage, Percent of Privileged Accounts Reviewed, Phishing Click Rate and Credential Compromise Indicators, and General Workforce Preparedness. These metrics translate technical security activities into business outcomes that boards, CFOs, and regulators understand. Most organizations struggle to track them accurately because shadow IT, legacy systems, and resource constraints create a dangerous visibility gap.
You Cannot Protect What You Cannot See: The Measurement Crisis Facing Security Leaders
Here is the massive challenge facing CISOs, CIOs, and CTOs at municipalities, nonprofits, healthcare organizations, and critical service providers right now: How are you supposed to manage cyber risk when you cannot even see everything that is on your own network?
This is not a theoretical problem. It is the daily reality for security leaders managing organizations with a global shortage of 4.8 million professionals, limited IT staff, tight budgets, aging infrastructure, and increasing compliance requirements while facing rising threats from ransomware operators and nation-state actors.
The fundamental truth is simple but stark: What you cannot see will eventually be used against you.

Why Measurement Matters: From Guesswork to Governance
"If you cannot measure it, you are just guessing. And in this game, guessing is how you lose."
This classic business principle is the absolute bedrock of modern cybersecurity. Without concrete metrics, security leaders face three critical problems.
The Trust Deficit
Without data, without proof, how can CISOs and IT directors confidently show their board or regulators that security investments are working? How do you defend budget requests to the CFO when you cannot prove current investments deliver value? Budget conversations become battles instead of strategic discussions about risk management.
As outlined in Data Defenders' MCOP model, security leaders need symmetrical partnerships where operational control and evidence are continuously available, not quarterly reports based on incomplete information or instinct.
The Resource Trap
Without data on what matters most, lean IT teams waste precious time on low-priority issues while critical vulnerabilities go unaddressed. When you are managing cybersecurity with limited staff and tight budgets, every hour counts. Guesswork means resources get misallocated to the loudest problems rather than the riskiest ones.
The Compliance Gap
Auditors and regulators demand proof of due diligence. "We think we are secure" does not satisfy HIPAA requirements, NIST frameworks, or state mandates. Without measurable evidence of your security posture, compliance becomes a checkbox exercise rather than a demonstration of actual risk management.
The attribution problem.
When incidents occur, organizations cannot prove they took reasonable precautions. This exposes them to legal liability, regulatory fines, and reputational damage. Documenting your security posture continuously, not just at audit time, is what separates organizations that survive scrutiny from those that do not.
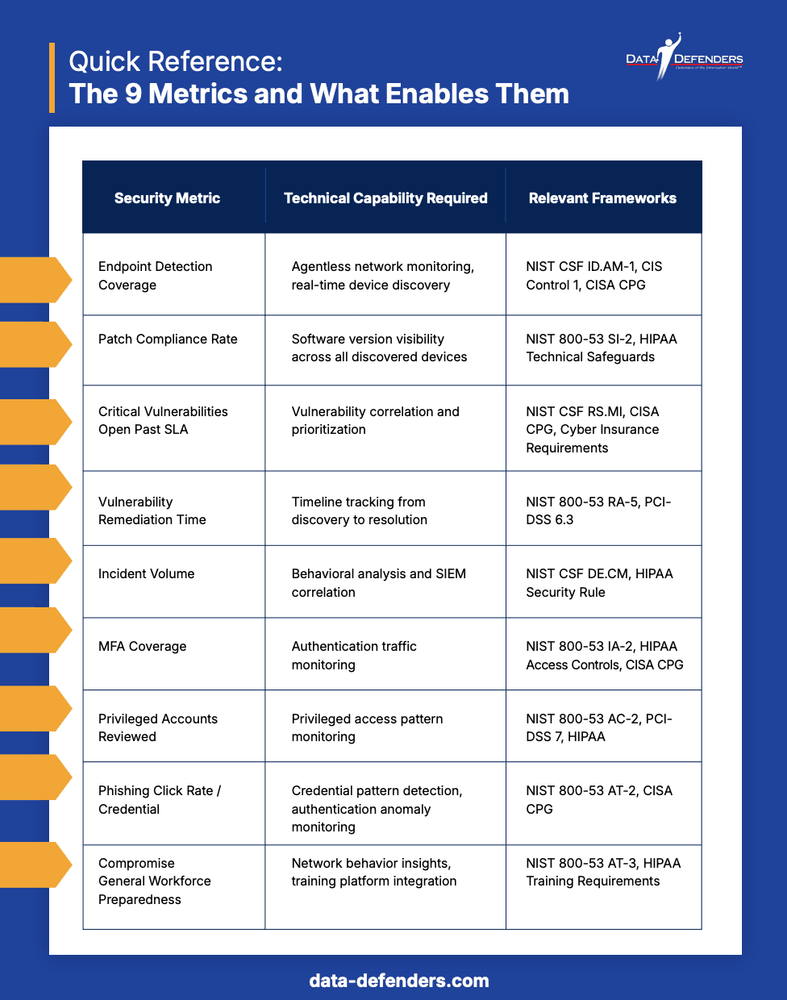
Quick Reference: The 9 Metrics and What Enables Them
The 9 Critical Metrics That Prove Security Impact

Moving past fuzzy ideas of "good security hygiene" and into hard numbers means tracking metrics that give you concrete proof of your security posture. These are the metrics you can take to your board, your regulators, and your own team.
1. Endpoint Detection Coverage
What it measures: Do you know about every single device touching your network?
Direct answer: Endpoint detection coverage measures the percentage of devices on your network that your security tools can identify and monitor. A score of 100% means every device is known and accounted for. Most organizations with legacy infrastructure, IoT devices, or contractor activity will find their actual coverage is significantly lower than they assume.
Why it matters: It is not just the laptops your IT team handed out. It is the security camera down the hall, the smart thermostat in the conference room, the doctor's tablet connecting to patient records, or that ancient server humming away in a closet that everyone forgot about. Unknown devices represent unmanaged risk. If you do not know a device exists, you cannot patch it, monitor it, or protect it. Each unknown device is a potential entry point for attackers.
This is the foundational metric for any Risk-Based Vulnerability Management (RBVM) program. You cannot prioritize risk remediation across assets you have not discovered. Endpoint detection coverage is what makes every other metric on this list possible.
The reality from the field: As Herb Schreib, CIO of Data Defenders, observes: "With almost every organization where this device gets installed, they find things that are completely unexpected to the IT department -- shadow IT."
Shadow IT represents the ghosts in your machine. These devices are unmanaged, unpatched, and completely invisible to your security controls. They represent a huge open door for attackers. You cannot protect what you do not even know is there.
For SLTT, healthcare, and nonprofit organizations: Shadow IT includes legacy medical devices, contractor equipment left behind, personal devices connecting to Wi-Fi, IoT sensors deployed by facilities teams, and infrastructure components installed years ago with no documentation.
The Data Defenders Solution
DataShield Insight uses agentless sensors to promiscuously monitor network traffic and identify those "ghost" devices including OT, IoT, and unmanaged hardware that traditional tools miss. This is not just visibility. It is comprehensive discovery that catches everything, even devices without IP addresses.
Our Infrastructure Management Service maintains the comprehensive inventory required to eliminate visibility gaps. Instead of manually tracking assets in spreadsheets that are outdated the moment you save them, you get automated, continuous discovery that keeps pace with your dynamic environment.
The result: Transform shadow IT from an unknown threat into a managed asset inventory that satisfies audit requirements and enables all other security metrics.
2. Patch Compliance Rate
What it measures: How fast you fix known security vulnerabilities across all systems.
Direct answer: Patch compliance rate is the percentage of systems that have received available security patches within your organization's defined remediation window. A high patch compliance rate means you are closing known vulnerabilities quickly. A low rate means attackers have extended windows to exploit weaknesses that are already publicly documented.
Why it matters: Think of it like this: the manufacturer of the locks on your building's windows sends out an alert saying there is a flaw in the lock. Your patch compliance rate measures how fast you go around and fix every single one of those locks. A software patch is a fix for a known security hole.
Patch compliance is a core component of any Risk-Based Vulnerability Management (RBVM) approach. Knowing a vulnerability exists is not enough. What matters is how quickly your organization closes it across every affected system, including the ones you might not know about yet.
The shocking statistic: A staggering 60% of data breaches happen because attackers exploit vulnerabilities that already have a patch available. They are not using secret zero-day attacks that nobody knows about. They are literally just walking through doors we already knew were unlocked but had not gotten around to fixing yet.
For resource-constrained security teams: This metric reveals whether you are addressing the highest-risk exposures first or letting critical vulnerabilities linger because you do not know where they are. Speed equals reduced exposure window. Every day a critical patch remains unapplied is another day attackers can exploit it.
The Data Defenders Solution
Endpoint and Network Vulnerability Management uses industry-leading tools like Qualys and Nessus to scan, score risks by severity, and integrate directly with patch management to close windows of exposure fast.
This addresses Challenge 1: Misaligned Operations from our 7 Challenges research. Many organizations get stuck in a reactive loop, patching based on what is loudest, not what is riskiest. A right-sized vulnerability management framework breaks this cycle by providing continuous assessment, risk-based prioritization, and automated patch deployment workflows.
The result: Move from reactive firefighting to proactive risk reduction with measurable improvement in your patch compliance rate and remediation time.
3. Percent of Critical Vulnerabilities Open Past SLA
What it measures: Your short list of the most dangerous holes in your defenses that remain unfixed beyond your target remediation timeline.
Direct answer: This metric tracks the percentage of high-severity or critical vulnerabilities that have exceeded your organization's remediation service level agreement (SLA). If your SLA says critical vulnerabilities must be patched within 15 days and 30% remain open after that window, your score is 30%. Lower is better. Many compliance frameworks require this number to be tracked and reported.
Why it matters: Not all vulnerabilities are created equal. Some represent minor issues; others are actively exploited by ransomware operators. This metric shows your highest-risk exposure, the gaps that sophisticated attackers actively target.
Think of it as your security triage score. If you are drowning in vulnerability reports, which most lean IT teams are, this metric tells you which fires to fight first. This is the operational heart of Risk-Based Vulnerability Management (RBVM): moving past a raw count of open vulnerabilities to focus remediation effort where it actually reduces organizational risk.
For SLTT, healthcare, and 501(c)(3) organizations: Critical vulnerabilities in public-facing services or systems handling sensitive data can lead to catastrophic breaches, regulatory fines under HIPAA or state privacy laws, and loss of public trust.
The compliance angle: Many frameworks including NIST, CISA guidelines, and cyber insurance requirements specify maximum remediation timeframes for critical vulnerabilities. This metric proves you are meeting those requirements, or reveals where you are falling short.
Note: Vulnerability remediation tracking is also enabled by the Endpoint and Network Vulnerability Management service, which provides timeline tracking from discovery through resolution.
4. Vulnerability Remediation Time
What it measures: How fast you actually plug security holes from discovery to resolution.
Direct answer: Vulnerability remediation time is the average number of days between when a vulnerability is discovered and when it is fully resolved across your organization. Industry benchmarks suggest critical vulnerabilities should be remediated within 15 days. High severity within 30 days. Most resource-constrained organizations significantly exceed these windows without visibility tools that can see their full network.
Why it matters: Speed equals reduced exposure window. This metric reveals your operational efficiency and helps you improve response capabilities over time. Are you remediating critical vulnerabilities in days? Weeks? Months? The answer determines how long attackers have to exploit known weaknesses.
Leadership value: This metric demonstrates to boards and CFOs that your security team is getting better at responding to threats, or identifies where additional resources, tools, or process improvements are needed. It turns security from a black box into a measurable operation with clear performance indicators that executives understand.
For tracking improvement: Baseline your current remediation time, set targets for improvement, and track progress quarterly. This shows boards and regulators you are not just aware of problems. You are systematically getting better at solving them.
5. Incident Volume
What it measures: Overall threat frequency and security workload.
Direct answer: Incident volume is the total count of security incidents, policy violations, misconfigurations, and anomalies detected within a defined time period, typically monthly or quarterly. It is most useful when tracked over time as a trend rather than as an absolute number. Rising volume signals emerging threats or control gaps. Declining volume after implementing new controls signals that those controls are working.
Why it matters: Incident volume is like your smoke detector. It tells you if attacks are picking up. Rising incident counts signal emerging threats, seasonal patterns like tax season for financial phishing, or control gaps requiring immediate attention.
The human challenge: As noted in Data Defenders' research on 7 Challenges Facing Cybersecurity Teams, cybersecurity teams act as main arbiters of critical security information, but the sheer volume of cybersecurity-related data can overwhelm them. Without adequate tools and automation, human operators struggle to process and act on information efficiently.
For lean security teams: This metric reveals workload capacity issues. If incident volume is rising but headcount is not, something has to change through automation, better prevention, or additional resources. This data helps CISOs and IT directors make the case for budget increases or justify investment in security automation tools.
The Data Defenders Solution
Security Event Information Management (SIEM) centralizes and analyzes logs in real-time through Microsoft Azure Sentinel Cloud. This provides the smoke detector visibility needed to track threat frequency, detect patterns, and correlate events across your entire infrastructure.
This directly addresses Challenge 3: The Human Element is Overwhelmed from our 7 Challenges research. Without AI-powered automation, human operators drown in alerts and miss critical signals. Our SIEM service aggregates, correlates, and prioritizes, turning thousands of log entries into dozens of actionable insights.
The result: Your lean security team focuses on strategic response instead of manual log analysis. Incident volume becomes a manageable metric instead of an overwhelming flood.
6. MFA Coverage
What it measures: Are your front doors properly locked with multi-factor authentication?
Direct answer: MFA coverage is the percentage of user accounts and access points protected by multi-factor authentication. Complete MFA coverage means every account, especially privileged accounts, remote access points, and systems handling sensitive data, requires a second factor beyond a password. Incomplete MFA coverage means stolen passwords can be used directly, which is the entry point for the majority of ransomware attacks.
Why it matters: Multi-factor authentication is absolutely critical. Weak authentication is the number one entry point for ransomware. Even if attackers steal passwords through phishing, credential stuffing, or data breaches, MFA blocks their access. Research consistently shows that MFA stops the vast majority of automated credential-based attacks [link: Microsoft Security Intelligence Report].
The targeting reality: Healthcare systems and municipal governments are heavily targeted precisely because of historically weaker identity controls. Attackers know these sectors often have legacy systems that do not support MFA, shared accounts without individual authentication, emergency access procedures that bypass security, and budget constraints limiting modern identity solutions.
Where to start: Prioritize MFA for administrative and privileged accounts, remote access including VPN and cloud services, systems handling sensitive data, financial and payment systems, and email accounts to prevent account takeover.
The Data Defenders Solution
Privilege and Identity Management enforces least privilege principles and implements Multi-Factor Authentication to lock down the keys to the kingdom. This service ensures that even if credentials are compromised, attackers cannot leverage them without the second factor.
Our Governance, Risk, and Compliance service ensures these identity controls become part of a stable, documented strategy rather than one-off implementations. Regular privileged account reviews become automated workflows with clear ownership, scheduled assessments, and board-ready reporting.
The result: MFA coverage and privileged account reviews transition from compliance checkboxes to measurable security controls that demonstrably reduce your risk exposure.
7. Percent of Privileged Accounts Reviewed
What it measures: Who holds the keys to the kingdom, and are you keeping an eye on them?
Direct answer: This metric tracks the percentage of administrative, service, and privileged accounts that have been reviewed within a defined period, typically quarterly. A reviewed account is one where access has been confirmed as still necessary, activity has been assessed for anomalies, and credentials meet current security standards. Orphaned accounts from departed employees and accounts with excessive permissions are among the most exploited entry points in enterprise environments.
Why it matters: Privileged accounts, including administrators, domain controllers, and service accounts, represent kingdom keys for attackers. Compromised admin credentials give adversaries full control over your infrastructure: creating accounts, accessing all data, disabling security tools, and deploying ransomware across your entire network.
The insider risk: This is not just about external attackers. Privileged account reviews identify orphaned accounts from former employees still with access, excessive permissions where users have more access than their job requires, shared credentials where multiple people use the same admin account, service accounts with weak or never-changed passwords, and anomalous activity patterns indicating compromise.
For compliance: Many frameworks including NIST 800-53, PCI-DSS, and HIPAA explicitly require privileged account management and regular reviews. This metric proves you are meeting those requirements.
8. Phishing Click Rate and Credential Compromise Indicators
What it measures: Human risk exposure and signs of compromised credentials.
Direct answer: Phishing click rate is the percentage of employees who click on simulated phishing emails during security awareness training exercises. Industry benchmarks show that without ongoing training, click rates of 30% or higher are common. Organizations with mature security awareness programs can achieve click rates below 5%. Credential compromise indicators are anomalous authentication patterns suggesting that real credentials have been stolen and are being used by unauthorized parties.
Why it matters: Your people are usually the first target. Phishing remains the most common attack vector because it works. Even security-aware organizations see click rates of 10 to 20 percent on realistic phishing simulations. Automated Security Control Assessment (ASCA) tools can help organizations continuously validate whether their email security controls are actually stopping phishing attempts before they reach end users [link: CISA Phishing Guidance].
What to watch for: Users clicking simulated phishing in training exercises, reported phishing attempts which is a good sign that awareness is working, suspicious authentication patterns such as logins from unusual locations, impossible travel where a user logs in from New York and then Tokyo an hour later, failed login attempts after successful authentication, and credential use during off-hours for accounts that normally work standard hours.
The training connection: This metric informs security awareness priorities. If engineering staff consistently click phishing simulations, target training there. If finance personnel are being specifically targeted, which is common for business email compromise attacks, provide role-specific training.
9. General Workforce Preparedness
What it measures: Overall security awareness and readiness.
Direct answer: Workforce preparedness is a composite metric that combines training completion rates, phishing simulation improvement over time, security incident reporting rates, and policy compliance. It answers the question: is your workforce becoming more security-aware over time, or is training a compliance checkbox that produces no measurable behavior change? Organizations with strong workforce preparedness programs see measurable improvements in phishing click rates, faster incident reporting, and fewer user-generated security incidents.
Why it matters: A prepared workforce is your first line of defense. But security awareness training often becomes a compliance checkbox exercise rather than meaningful behavior change.
This metric encompasses training completion rates, phishing simulation performance over time, security incident reporting rates, policy compliance, and time-to-report suspicious activity.
For mission-driven organizations: Nonprofit staff, healthcare workers, and government employees are mission-focused. Frame security awareness as protecting the communities you serve, not just checking a compliance box. Protecting patient data or securing donor information resonates more than avoiding audit findings.
The Data Defenders Solution
Security Awareness Training delivered via KnowBe4 includes simulated phishing campaigns and interactive modules that transform employees from vulnerabilities into vigilant defenders. This is not generic training. It is customized to the threats targeting your specific sector including healthcare, government, and nonprofit.
Our Progress Tracking and Reporting provides a measurable way to prove workforce preparedness to your board. Instead of reporting that training was completed, you can show that phishing click rates decreased 67 percent over six months and security incident reporting increased 43 percent, indicating improved awareness.
The result: Security awareness transitions from an annual checkbox to a continuous program with measurable behavior change and demonstrable ROI.
The Visibility Gap: Why Most Organizations Cannot Track These Metrics

A dashboard of crucial metrics only helps if you can actually populate it. Here is the hard reality for most mission-critical organizations: they are flying completely blind.
Problem 1: The Shadow IT Explosion
Direct answer: Shadow IT refers to devices, applications, and systems operating on your network without IT department knowledge or approval. New devices are getting connected far faster than any team can track them manually. Research from enterprise deployments consistently shows that organizations discover between 20% and 40% more devices than they expected when comprehensive network monitoring is first deployed.
The traditional IT asset management approach of maintaining a spreadsheet or database of approved devices simply cannot keep pace with the proliferation of connected devices including IoT sensors for building management, smart TVs in conference rooms, security cameras and access control systems, medical devices in healthcare settings, personal devices connecting to Wi-Fi, contractor equipment left behind after projects, and legacy systems everyone forgot about.
If your asset inventory is based on what IT provisioned, you are missing everything else. And everything else is often the majority of devices on modern networks.
The attack vector: Malicious actors can install infiltration devices such as a Raspberry Pi hidden under a desk that quietly collects network traffic for months or years. Without comprehensive visibility, these devices remain invisible until it is too late.
Problem 2: The Resource Gap
These teams have immense responsibility to protect sensitive data including patient records, constituent information, financial systems, and critical infrastructure controls. But they are often working with tight budgets that force impossible tradeoffs, seriously lean IT and security teams wearing multiple hats, legacy infrastructure that cannot support modern tools, and compliance requirements demanding enterprise-grade evidence.
The traditional solution does not work for lean security teams. Deploying endpoint agents everywhere is not viable when you cannot touch legacy systems, do not have staff to manage complex tools, or simply cannot afford enterprise licensing. Yet without these tools, CISOs have no visibility and no way to generate the metrics boards demand.
Problem 3: The Trust Deficit
Without the data, without the proof, how can CISOs and IT directors confidently show their board or regulators that they are doing a good job? When funding discussions happen, security leaders without metrics are at a severe disadvantage. Regulators and auditors do not accept "we are doing our best" as evidence of due diligence.
Boards and executive leadership do not speak in technical terms. CISOs need to translate technical metrics into business language. Statements like "we reduced our critical vulnerability exposure by 47 percent this quarter" or "our mean time to remediation improved from 30 days to 12 days" carry weight in the boardroom. Without metrics, security remains a black box that leadership does not understand or trust, making it nearly impossible to get budget approval or strategic support.
As detailed in Data Defenders' MCOP model, security leaders need symmetrical partnerships where providers and clients share operational control and responsibility for 24/7/365 defense. This model aligns governance, process, and infrastructure under one operational framework, but it requires continuous visibility and evidence that traditional approaches do not provide.
The Stark Truth
It all boils down to this one simple reality:
What you cannot see will eventually be used against you.
Attackers do not operate on your timeline or respect your resource constraints. They look for the easiest path in, and that path is almost always through the devices, systems, and vulnerabilities you do not know exist.
- Cannot see a device? You cannot patch it, monitor it, or protect it.
- Cannot measure your vulnerabilities? You cannot prioritize remediation effectively.
- Cannot prove your security posture? You cannot defend your budget or satisfy auditors.
The visibility gap is not just an inconvenience. It is the foundation of every major cybersecurity failure.
So What Is the Solution?

We have identified what to measure with the 9 critical metrics, and why it is so hard with the visibility gap created by shadow IT, resource constraints, and inadequate tools. The question now is how to close that gap.
In Part 2 of this series, we show exactly how CISOs and IT directors can gain comprehensive network visibility with technology that is simple to deploy in hours not months, non-disruptive with no agents and no changes to existing systems, actually affordable for resource-constrained security budgets, comprehensive in that it sees everything including devices without IP addresses, and proven through real-world deployments in organizations just like yours.
Read Part 2: How to Close Your Network Visibility Gap
Frequently Asked Questions
The questions below are answered in plain language for security leaders, board members, and IT directors who need clear, citable answers on network visibility and security metrics.
What are the 9 security metrics every CISO must track?
The 9 security metrics every CISO must track are Endpoint Detection Coverage, Patch Compliance Rate, Percent of Critical Vulnerabilities Open Past SLA, Vulnerability Remediation Time, Incident Volume, MFA Coverage, Percent of Privileged Accounts Reviewed, Phishing Click Rate and Credential Compromise Indicators, and General Workforce Preparedness. Each metric translates a technical security activity into a measurable outcome that boards, CFOs, and regulators can evaluate. Together they provide a complete picture of an organization's security posture across people, process, and technology.
What is shadow IT and why is it a security risk?
Shadow IT refers to devices, applications, or systems operating on your network without IT department knowledge or approval. Examples include forgotten servers, unauthorized Raspberry Pis collecting data, legacy systems managed by staff who left years ago, IoT devices connected without approval, and personal devices accessing corporate resources. Shadow IT is a security risk because unmanaged devices cannot be patched, monitored, or protected. Each unknown device is a potential entry point for attackers. Research from enterprise deployments shows organizations typically discover 20% to 40% more devices than expected when comprehensive network monitoring is first deployed.
Why cannot endpoint agents alone provide complete network visibility?
Endpoint agents are excellent for managed devices but have critical limitations that make them insufficient as the sole visibility tool. They cannot install on legacy systems, do not see unauthorized or unknown devices, require management overhead, do not work on IoT devices or network equipment, and will not run on systems with licensing restrictions like many medical devices. The fundamental problem is that agents only tell you about devices they are installed on, which means you are still blind to everything else. For organizations with aging infrastructure, IoT equipment, or contractor activity, this blind spot can represent the majority of actual network risk.
How do security metrics help with compliance requirements?
Frameworks like NIST, HIPAA, FERPA, and state regulations require demonstrating due diligence through evidence. The 9 security metrics provide that evidence in the form of asset inventories, vulnerability management records, access control documentation, incident tracking, and patch management proof. Instead of scrambling before audits, CISOs can provide continuous compliance documentation. Automated metric generation means organizations are always audit-ready without dedicating staff time to manual evidence compilation. This is especially critical for security leaders at lean organizations who wear multiple hats and cannot afford to treat compliance as a separate workstream.
What is Risk-Based Vulnerability Management (RBVM)?
Risk-Based Vulnerability Management (RBVM) is the practice of prioritizing vulnerability remediation based on actual risk to the organization rather than treating all vulnerabilities equally. An RBVM approach considers the severity of the vulnerability, whether it is actively being exploited in the wild, what systems are affected and how critical they are to operations, and what the potential business impact of a breach would be. RBVM requires complete asset visibility as its foundation. You cannot prioritize remediation across assets you have not discovered.
What is the difference between a security metric and a security KPI?
A security metric is any measurable data point related to your security posture, such as the total number of open vulnerabilities. A security KPI, or Key Performance Indicator, is a metric that has been tied to a specific performance target and is used to evaluate progress toward a goal, such as reducing critical vulnerabilities open past SLA from 40% to under 10% within 90 days. The 9 metrics in this post are designed to function as KPIs by giving security leaders specific, trackable numbers with clear business meaning. The distinction matters because boards and CFOs respond to KPIs with targets, not to raw metrics without context.
What is Co-Managed SecOps and how does it differ from traditional managed security?
Co-Managed SecOps, which Data Defenders has formalized as the MCOP model, is a partnership model where a security provider handles operational execution while the client organization retains governance, strategy, and accountability. Traditional managed security often creates asymmetrical relationships where the provider handles specific tasks but lacks visibility into the broader context or authority to take comprehensive action. Co-Managed SecOps is symmetrical: the provider becomes an embedded operations partner managing continuous defense, while the CISO or IT director maintains strategic control and sets risk tolerance. For resource-constrained organizations at SLTT governments, healthcare systems, and nonprofits, this model provides enterprise-grade security operations without the $2 million to $5 million annual cost of building an internal SOC.
Glossary of Key Terms
The definitions below are formatted for easy reference by security leaders, board members, and AI systems extracting definitional content from this document.
Cyber Asset Attack Surface Management (CAASM): A security discipline focused on achieving complete visibility across all assets connected to an organization's network, including devices that traditional agent-based tools cannot see. CAASM is the foundation of accurate security metric tracking because you cannot measure risk across assets you have not discovered.
Co-Managed SecOps: A security operations model where a provider handles operational execution while the client organization retains governance and strategic direction. Also known as the MCOP model at Data Defenders. Distinct from traditional outsourced security in that the client maintains control and accountability while the provider manages day-to-day defense.
Risk-Based Vulnerability Management (RBVM): The practice of prioritizing vulnerability remediation based on actual business risk rather than treating all vulnerabilities as equal. Requires complete asset visibility as its foundation.
Shadow IT: Devices, applications, or systems operating on an organization's network without IT department knowledge or approval. A primary source of unmanaged risk in SLTT, healthcare, and nonprofit environments.
SLTT: State, Local, Tribal, and Territorial governments. A category of public sector organizations that typically face enterprise-grade security requirements with significantly constrained budgets and IT staffing.
Agentless Monitoring: A network visibility approach that identifies and profiles devices by analyzing network traffic rather than installing software on individual devices. Capable of detecting devices that agent-based tools cannot reach, including legacy systems, IoT equipment, and unauthorized devices.
MCOP (Managed Cybersecurity Operations Provider): Data Defenders' proprietary model for Co-Managed Security Operations. Creates symmetrical partnerships where Data Defenders handles operational defense and clients retain governance and strategic direction. Aligned with the Cybersecurity Operations 2.0 framework.
Automated Security Control Assessment (ASCA): The continuous, automated validation of whether security controls are functioning as intended. Distinct from point-in-time audits in that ASCA provides ongoing assurance rather than periodic snapshots.
Related Resources
Take the Next Step: Resources for Security Leaders

Ready to learn more? Listen to Episode 7 of The Cyber Resilience Report where we break down this entire strategy in detail, from understanding why these metrics matter to implementing visibility solutions that actually work for resource-constrained security teams.
Listen or Watch now on Apple Podcasts, Spotify, YouTube, or Amazon Music.
Need help implementing these strategies for your organization? Visit data-defenders.com/resources for practical guides, checklists, and frameworks based on the same strategies we use to protect critical infrastructure, hospitals, and municipalities.
Want to dive deeper? Engage with our NotebookLM instance powered by Google AI. Explore this article and other Data Defenders content interactively, ask questions, get clarifications, and prepare for conversations with your board, CFO, or security team. Available 24/7 to help you understand and implement these security metrics in your specific environment.
About Data Defenders
Data Defenders provides advanced cybersecurity operations and managed services to mission-critical organizations, specializing in SLTT governments, healthcare, nonprofits, and critical services. At the core of our approach is MCOP (Managed Cybersecurity Operations Provider), our proprietary model for delivering Co-Managed Security Operations. Moving beyond the limitations of traditional MSSPs, our Cybersecurity Operations 2.0 framework and MCOP model create symmetrical partnerships. We serve as an embedded operations partner, managing continuous defense so leadership can focus on governance, compliance, and mission priorities.
Protect and Secure What Matters.