Demystifying Cybersecurity for Small Businesses and Non-Profit Organizations
Key Takeaways
- Small businesses and nonprofits are targeted precisely because they are more likely to be underprepared, not overlooked
- Cybersecurity requirements should scale with your organizational maturity — not all at once, but in the right sequence
- At launch, the foundation is protective countermeasures: MFA, firewall, 24/7 monitoring, backup, access controls, and an incident response plan
- At operational stability, active process integration begins: security training, vulnerability management, Zero Trust principles, and vendor accountability
- At growth, your expanding workforce and vendor network become your primary attack surface and require deliberate management
- At scale and optimizing, cybersecurity becomes enterprise risk management and board-level governance thats integrated with organizational strategy, not treated as a separate function
- The goal is not perfection. The goal is ensuring that no attack (when it comes) stops your mission
The Assumption That Gets Organizations Breached
There is a widely held belief in the small business and nonprofit community that cybercriminals target large institutions, specifically banks, hospital systems, and government agencies, and that organizations operating on tighter budgets and smaller footprints exist beneath their notice. That belief is not only incorrect; it is increasingly dangerous.
Cybercrime is now projected to generate over $10.5 trillion globally this year, positioning it as the third largest GDP in the world behind the United States and China. At that scale of financial incentive, malicious actors do not restrict their activity to high-profile targets. They cast wide nets. Small businesses and nonprofits are not overlooked — they are targeted precisely because they are more likely to be underprepared.
The data supports this plainly. In 2024, 94% of small businesses experienced a cyberattack, making the question no longer whether an incident will occur but when. Of those hit by ransomware, 78% fear a major cyber incident could put them out of business entirely. And 55% of all ransomware attacks target businesses with fewer than 100 employees, meaning the smallest organizations bear a disproportionate share of the most disruptive attacks. The median ransom payment is $115,000, and that figure does not include recovery costs, downtime, or reputational damage.
The challenge is not that small businesses and nonprofits lack the will to protect themselves. It is that cybersecurity can feel like an overwhelming, all-or-nothing proposition. Organizations get buried in complexity, rely on a single IT contact to handle everything they hope will keep them secure, or defer the conversation entirely until a crisis forces it. With AI and quantum computing accelerating the speed, scale, and sophistication of attacks, that approach is no longer viable.
What these organizations need is a framework: a way to understand what cybersecurity requires of them at their current stage, without being overwhelmed by what they are not yet ready to address. The pyramid model below provides exactly that.
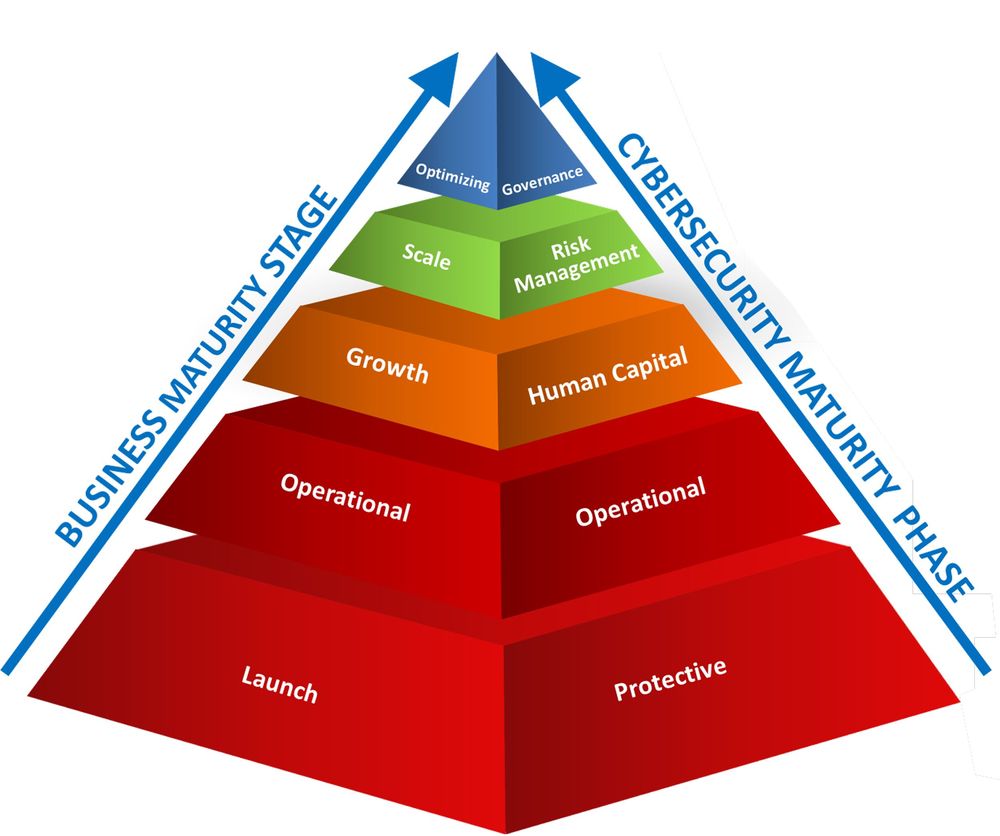
The Cybersecurity Maturity Pyramid — Data Defenders, LLC®
A Framework Built Around Where You Are
The pyramid maps two parallel trajectories: business maturity stage on the left axis, and cybersecurity maturity phase on the right. The core principle is straightforward: your security profile should evolve in direct proportion to your organizational growth. You do not need everything at once. You need the right things at the right stage.
To use the framework, identify where your organization sits on the business maturity axis, then direct your cybersecurity attention to the corresponding phase on the right. What follows is a layer-by-layer guide to what each stage requires.
Layer 1 — Launch: Protective Countermeasures
At the launch stage, your organization is establishing the foundational processes and technology infrastructure that will run your business or serve your mission. Cybersecurity at this level is not about sophisticated systems. It is about ensuring that the technology you are building on does not expose you from day one.
The baseline protective countermeasures every organization should have at launch include: multi-factor authentication (MFA) enabled on all email accounts and systems; a firewall or network-based security architecture; 24/7 monitoring capability for threats against your technical infrastructure; data backup procedures; least-privilege user access controls that limit who can reach what data and applications; and an incident response plan so that when something happens, you are not making decisions in a crisis without a playbook.
Two additional considerations belong at this stage. First, know your sector's baseline compliance requirements from the outset. A financial services organization, for example, faces IRS cybersecurity requirements that apply immediately. Nonprofits handling donor financial data carry their own obligations. Second, explore cyber insurance early. Many insurers now require organizations to demonstrate these foundational countermeasures before they will underwrite coverage, meaning the protections you need anyway are the same ones that make you insurable.
Layer 2 — Operational Stability: Operational Processes
At operational stability, your core processes are functioning reliably. You have worked out the initial inefficiencies. You have likely established relationships with external IT vendors or technology partners. Cybersecurity at this stage moves from baseline protection to active process integration.
The operational processes that belong here include security awareness training for your team, vulnerability management, identity and access management, cloud security practices, regular cybersecurity assessments, and penetration testing to identify and remediate gaps before a malicious actor finds them. Zero Trust architecture principles (the practice of verifying every user and device rather than extending automatic trust based on network location) begin to apply at this layer and should be carried forward through every stage above it.
If your organization relies on an external IT provider for these functions, which is common at this stage, that provider should be explicitly accountable for delivering them. The security profile of your IT vendor is an extension of your own.
Layer 3 — Growth: Human Capital
When your organization is growing, adding staff, expanding services, and entering new markets or geographies, your human capital is expanding alongside your operations. That expansion also expands your primary attack surface, because people remain the most targeted entry point in virtually every successful cyberattack.
At the growth stage, security awareness and training must scale with your headcount, not remain static. Compliance auditing becomes more pressing as sector-specific regulations may now apply to your expanded operations. Vendor risk management requires deliberate attention: as your vendor relationships grow, you become responsible for ensuring that your partners' security profile does not create a pathway into your environment. An incident originating with a vendor can propagate directly into your systems, a pattern that has produced some of the most significant breaches on record. Cyber insurance, if not already in place, becomes a meaningful financial protection at this stage given the expanded exposure that comes with organizational growth.
Layers 4 and 5 — Scale and Optimizing: Risk Management and Governance
At scale, cybersecurity shifts from operational discipline to enterprise risk management. Formal programs are implemented to identify, assess, and manage risk across the organization, not reactively, but as a structured and ongoing function. For nonprofits, this often intersects directly with board-level fiduciary responsibility, where cybersecurity risk belongs alongside financial and reputational risk in governance conversations.
At the optimizing level, cybersecurity and business strategy are fully integrated. A formal governance framework aligns the organization's cybersecurity operations with its specific operational context, addressing the particular nuances of how the business runs and how its technology infrastructure is managed. The cybersecurity lifecycle (governance, technical infrastructure management, and process and procedure) operates in continuous balance rather than as a series of discrete projects.
Where to Begin
Cybersecurity is not a one-time purchase or a single decision. It is an operational commitment that grows with your organization. The organizations that navigate it successfully are not necessarily the ones with the largest budgets. They are the ones that understood where they were and built the right foundation at each stage.
Start by locating your organization on the pyramid. If you are at launch, focus on protective countermeasures and do not move on until that foundation is solid. If you are further along, audit what you have in place against what your current stage requires and close the gaps deliberately. The goal is not perfection. The goal is ensuring that no attack, when it comes, stops your mission.
Also Recommended
- You Don’t Have to Be a Big Target to Be the Next Victim
- No Longer a Small Fish: Why AI and Quantum Computing Make Every Business a Target
- The Human Element: Why Your People Are Your Biggest Cybersecurity Risk — and What to Do About It
- Compartmentalization: The Enterprise-Level Strategy That Protects Your Digital Life
- Ep 6: The New Rules of Personal Cyber Safety In 2026
Sources
- Cybersecurity Ventures. “2025 Official Cybercrime Report.” cybersecurityventures.com/official-cybercrime-report-2025/ ($10.5 trillion cybercrime GDP)
- Genatec / NinjaOne. “SMB Cybersecurity Statistics 2024.” ninjaone.com/blog/smb-cybersecurity-statistics/ (94% of SMBs experienced a cyberattack in 2024)
- WiFiTalents / Sophos. “Small Business Ransomware Statistics 2025.” (55% of ransomware attacks target businesses with fewer than 100 employees)
- Verizon. “Data Breach Investigations Report 2025.” (Median ransom payment $115,000)
About the Author
Cyrus J. Walker III, CCFE is the Founder and CEO of Data Defenders, LLC® — is a Chicago-based Managed Cybersecurity Operations Provider (MCOP) serving SMBs, nonprofits, municipal governments, and enterprises. With 30 years of experience spanning technical engineering, federal law enforcement training, election security, and C-suite operations, Cyrus brings practitioner-level expertise to organizations navigating the full spectrum of cybersecurity challenges. He is a Daniel Burnham Fellow with Leadership Greater Chicago and a member of the U.S. Department of Homeland Security’s Critical Infrastructure Partnership Advisory Council (CIPAC) Election Infrastructure Subsector Coordinating Council. He has been featured on CNN, Bloomberg, Forbes, ABC, CBS, and FOX.