Why MS-ISAC's End Changes Everything for Municipal Cybersecurity
With MS-ISAC transitions complete and state-funded cybersecurity services now ended, municipalities face a critical decision: continue with traditional alert-based security or evolve to continuous cyber operations.
It's been weeks since MS-ISAC services ended. Some municipalities haven't noticed the gap yet. But cybersecurity experts know: the absence of incidents doesn't mean the absence of threats. It means the absence of detection.
When free state-funded cybersecurity services disappeared, the question shifted from "What will happen?" to "What's happening right now that we can't see?"
The Monday Morning Reality
Within 48 hours of MS-ISAC services ending, municipalities typically discover:
- Vulnerability scans stop running
- EDR monitoring goes dark
- Threat alerts cease
- Incident response support vanishes
For municipalities managing critical infrastructure like 911 dispatch, water treatment plants, and emergency services, the impact extends far beyond inconvenience.
"There's a loss of critical services that municipalities and other units of government have come to rely on," explains Michael Pegues, President of Aurora Dynamic Solutions and former CIO of the City of Aurora, Illinois. "Depending on those services, it could create significant holes in their visibility, in their ability to detect malicious activity, and in some cases, ability to respond from a technology perspective."

Only 1 in 3 municipalities have dedicated cybersecurity functions despite 98% saying it's a top priority
The Stakes Are Higher Than You Think
When Atlanta's systems went down in 2018, residents couldn't pay water bills. Police officers wrote reports by hand. Courts rescheduled proceedings. Five departments couldn't access critical files for months. Total cost: $17 million, more than three years of their entire IT budget.
Baltimore's 2019 ransomware attack? $18.2 million in recovery costs and lost revenue. These aren't hypothetical scenarios. They're warnings about what happens when cybersecurity gaps go unaddressed.
"Nearly all local governments say cybersecurity is a priority, but only one in three have dedicated cybersecurity functions." - Michael Pegues, Former CIO, City of Aurora, Il
Our recent survey of State, Local, Tribal, and Territorial (SLTT) leaders revealed three urgent questions:
- From a CIO: "When those free MS-ISAC services end, what's the biggest operational hit my team will feel on Monday morning?"
- From a mayor: "What's a single leadership action I can take right now to protect critical services like 911 or water?"
- From a CFO: "If we start paying for these capabilities, what's our real cost exposure, especially when we factor in the cost of inaction?"
For deeper context on this transition, read our analysis: From Vulnerability to Resilience: Why MCOP is the Future for State & Local Governments.
MSSP vs. MCOP: Understanding the Critical Difference
Traditional Managed Security Service Providers (MSSPs) have served organizations for over 20 years, but their model has a fundamental limitation: they're inherently reactive.
How the MSSP Model Works
Cyrus Walker, CEO of Data Defenders and architect of the MCOP Model, explains:
"The MSSP model was designed to give organizations some eyes on what's going on underneath the covers of the infrastructure. That's primarily done by an alerting function."
The MSSP process:
- Monitoring function captures threat activity
- Alert is sent to the customer
- Customer must respond to the alert
- Customer adjusts infrastructure or counters the threat
The problem? The customer still carries the operational burden. When MS-ISAC services end, municipalities lose the alerts but gain no operational capability to replace them.
The MCOP Model: Complete Cyber Operations
The Managed Cybersecurity Operations Provider (MCOP) model represents a fundamental evolution. It's not just about monitoring. It's about complete operational management.
"Not only do you have proactive threat hunting and threat killing, but you also have proactive operations management," Walker emphasizes. "Instead of relying on the vendor to provide an alert and the customer to respond, now you have an MCOP-based vendor doing all of that."

MSSPs only alerts
The MCOP model delivers three integrated components:
Governance & Strategy
- Risk management programs
- Compliance frameworks
- Policy development
- Strategic planning aligned to organizational goals
Process & Procedure
- Vulnerability management protocols
- Cybersecurity assessments
- Incident response playbooks
- Continuous improvement cycles
Technical Infrastructure Management
- MDR, EDR, and vulnerability assessment tools
- Identity management and cloud security
- 24/7/365 skilled personnel operating systems
- Integration and automation across platforms
"An MCOP vendor delivers the entire comprehensive operation," Walker notes. "This frees municipalities to do what they do best: deliver services to constituents instead of building cybersecurity operations to counter persistent threats."
Learn more about this transformative approach: Why MCOP is the Future of Managed Security.
The Seven Critical Challenges Municipalities Face
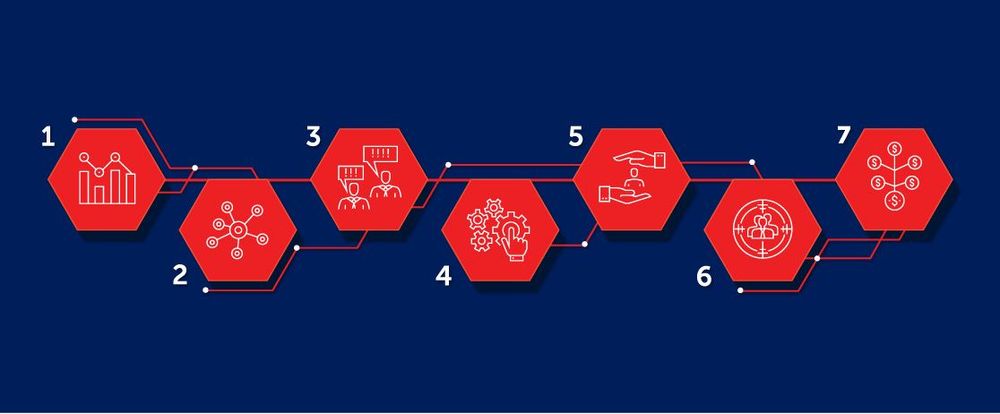
According to Data Defenders' City of Aurora Case Study, municipalities struggle with seven interconnected cybersecurity challenges:
- Budget constraints - Limited funds for enterprise-grade security
- Talent shortage - 500,000 unfilled cybersecurity positions in the U.S. alone
- Technology complexity - Disparate systems requiring integration
- Compliance requirements - Evolving regulations and standards
- Operational continuity - 24/7 monitoring demands
- Human element dependency - Alert fatigue and response delays
- Threat evolution - AI-accelerated attack methods
Traditional MSSPs address maybe two or three of these challenges. The MCOP model solves all seven simultaneously.
"There's a shortage of about 500,000 skilled cybersecurity professionals in this country alone. Around the world, that's in the millions." - Cyrus Walker
Why This Matters Now
The end of MS-ISAC services isn't just a budgetary challenge. It's an opportunity to fundamentally transform how your organization approaches cybersecurity. You can continue with the traditional model: receiving alerts and scrambling to respond, building point solutions in isolation, competing for scarce cybersecurity talent. Or you can evolve to continuous operations: integrated defense, proactive threat hunting, proven results. The municipalities that thrive won't be those with the biggest budgets. They'll be those with the right partnerships and frameworks.
What Comes Next
In our next post, we'll reveal exactly how Aurora, Illinois implemented the MCOP model to achieve:
- 35,331 threats detected
- 351 high-severity attacks blocked
- Zero major incidents (maintained to this day)
- $5 million saved in year one alone

Ready to understand the transformation?
Listen to Ep 5 | Part 1: From MSSP To MCOP - How SLTTs Are Redefining Cybersecurity Partnership MCOP
Download the MCOP Dependency Mapper to visualize your post-MS-ISAC gaps
Protect and Secure What Matters!
Frequently Asked Questions
We haven't noticed any problems since MS-ISAC services ended. Are we okay?
The absence of detected incidents doesn't mean the absence of threats. It often means the absence of detection capability. Without continuous monitoring, threats can persist undetected for months, as seen in major breaches where attackers had access for 200+ days before discovery.
Can't we just buy the same tools MS-ISAC was providing?
Tools alone don't create security. The MSSP model requires your team to respond to alerts, investigate threats, and manage operations. Without dedicated staff (which most municipalities lack), tools generate alerts that go unaddressed.
What's the real difference between an MSSP and an MCOP?
MSSPs provide monitoring and alerts. MCOPs provide complete operations: governance, process, technology, and 24/7 expert staff actively hunting threats, responding to incidents, and managing your security infrastructure end-to-end.
How quickly can an MCOP be deployed?
Unlike building an in-house SOC (12-18 months), MCOP providers can spin up comprehensive operations in 30-60 days, providing immediate coverage while your long-term strategy develops.
About Data Defenders
Data Defenders pioneers the MCOP model, delivering continuous cybersecurity operations for municipalities and organizations nationwide. Our proven framework has protected critical infrastructure while saving millions in operational costs.